Critical Google Kubernetes Engine Vulnerability Exposes 250,000 Clusters: Threat Actors Could Seize Control with Google Account
Plus, Ransomware Group Kasseika Employs BYOVD Tactic to Disable Security Processes on Windows Hosts
Security Alert: Sys: All Flaw in GKE Puts 250,000 Active Clusters at Risk of Unauthorized Takeover
A critical vulnerability named Sys:All has been uncovered in Google Kubernetes Engine (GKE), putting an estimated 250,000 active clusters at risk of unauthorized takeover. Discovered by cloud security firm Orca, the flaw arises from a widespread misconception regarding the system:authenticated group in GKE, allowing any Google-authenticated account (even outside the organization) to be included. Security researcher Ofir Yakobi notes that this misconfiguration, if exploited, could enable external threat actors with a Google account to seize control of the Kubernetes cluster.
The system:authenticated group, meant to include verified and deterministic identities, includes all authenticated entities, including human users and service accounts. Exploiting this loophole could lead to severe consequences, enabling threat actors to perform lateral movement, engage in cryptomining, execute denial-of-service attacks, and steal sensitive data without leaving traceable links to the originating Gmail or Google Workspace account.
The attack vector could expose various sensitive data, such as JWT tokens, GCP API keys, AWS keys, Google OAuth credentials, private keys, and credentials to container registries. Following responsible disclosure to Google, the company has taken steps to address the issue, blocking the binding of the system:authenticated group to the cluster-admin role in GKE versions 1.28 and later. Google recommends users avoid binding the system:authenticated group to any RBAC roles and assess and remove unsafe bindings.
While there is no public record of large-scale attacks exploiting this vulnerability, Orca warns that it could be a matter of time, underscoring the need for users to take immediate steps to secure their cluster access controls. The improvement in GKE versions is acknowledged, but the company emphasizes the continued existence of other roles and permissions that can still be assigned to the system:authenticated group, urging heightened security measures.
Emerging Threat: Kasseika Ransomware Utilizes Bring Your Own Vulnerable Driver (BYOVD) Attack for Effective Security Disarmament
The ransomware group Kasseika has adopted the Bring Your Own Vulnerable Driver (BYOVD) attack, following in the footsteps of other threat actors like Akira, AvosLocker, BlackByte, and RobbinHood. Identified by cybersecurity firm Trend Micro in mid-December 2023, Kasseika demonstrates similarities with the now-defunct BlackMatter ransomware, raising suspicions of a potential connection. The BYOVD tactic allows threat actors to terminate antivirus processes and services, facilitating the deployment of ransomware on compromised Windows hosts.
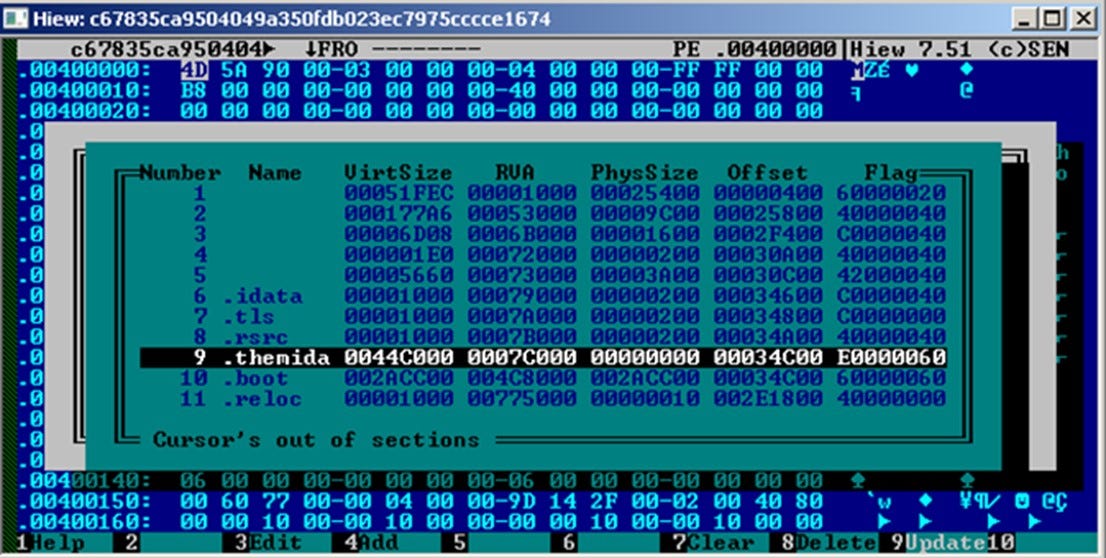
Kasseika's attack chain begins with a phishing email for initial access, deploying remote administration tools (RATs) to gain privileged access and move laterally within the target network. The threat actors employ Microsoft's Sysinternals PsExec utility to execute a malicious batch script, checking for the existence of the "Martini.exe" process and terminating it if found. The subsequent download and execution of the "Martini.sys" driver aim to disable 991 security tools.
The ransomware payload, named "smartscreen_protected.exe," then initiates the encryption process using ChaCha20 and RSA algorithms, terminating processes and services accessing Windows Restart Manager. Kasseika demands a 50 bitcoin payment within 72 hours, threatening an additional $500,000 every 24 hours after the deadline. Victims must post a payment screenshot to an actor-controlled Telegram group to receive a decryptor.
Additionally, Kasseika wipes traces of its activity by clearing the system's event logs using the wevtutil.exe binary, enhancing the challenge for security tools to identify and respond to malicious activities. This development underscores the evolving tactics of ransomware groups, emphasizing the need for robust cybersecurity measures to thwart sophisticated attacks.
Jobs/Internships
Zip Co - Software Engineer, Core Product - Sydney, New South Wales, Australia
Coinbase - Site Reliability Engineer - Client Platform - Fully Remote
BlackSky - Senior Machine Learning Engineer - Fully Remote
SpaceX - Summer 2024 Software Engineering Internship/Co-op - On-site
NeuraFlash - UX Design Intern - United States, NY · On-site
T-Mobile - Summer 2024 Data Science Internship - Bellevue, WA